In this world of nosy corporations and government spies, it would be really nice to have a secure, anonymous, decentralized messenger app to communicate with. Like many privacy advocates, this is the vision that drew me to try Session messenger more than a year ago.
Unfortunately, Session wasn't really ready back then. It was slow, buggy, and unreliable. I'm glad to say that the team didn't give up, and in fact have made numerous major improvements to their product since that time. Overall we were impressed when testing and researching the product for this new Session messenger review.
Session messenger basics
As the company puts it,
Session is an end-to-end encrypted messenger that minimizes sensitive metadata, designed and built for people who want absolute privacy and freedom from any form of surveillance.”
That could be a description of Signal messenger. And that shouldn't be a surprise, since Session began life as a fork of Signal. But Session has evolved far from there. Signal is a super-secure, centralized messaging service. Session is an anonymous, private, decentralized messaging system. There's a big difference.
There are no central servers in Session. Apps communicate through an onion routing network (similar to Tor) comprised of thousands of independent nodes. These nodes are part of Oxen, a decentralized, censorship resistant, trustless network*. You don't need to know how Oxen works, beyond the fact that it makes Session anonymous and decentralized.
* If you want to learn more about Oxen and the blockchain magic it does behind the scenes, here's a link to the Oxen website.
Session also was designed to expose the absolute minimum of metadata. Metadata is the data about the messages that flow back and forth between your app and that of whomever you are communicating with.
Metadata doesn't expose the content of your messages. But depending on the design of the messenger app, metadata can tell snoops all sorts of things that you probably wouldn't want to be exposed. Things like who you talk to, when and how long you talked to them, what kind of device you are communicating with, your operating system, mobile device battery status, even your IP address. Clever enemies can do a lot with that kind of metadata, and the less of it outsiders have, the more privacy you have.
Session addresses this problem in a few ways. They don't require you to enter an email address or phone number to create an account. You can't, even if you want to. The app generates a random Session ID that has no connection with any personal information.
Session also functions without gathering any metadata about your activities. Even if they wanted to, thanks to Oxen, there are no central servers on which to log such data.
As you can see, Session arrived on the scene with a bright vision and a bunch of shiny technology. But none of it worked very well. That's what the Session team has been working on for the last few years.
Now Session works smoothly. It uses end-to-end (E2E) encryption for everything: sending text and voice messages, sharing files, images, and attachments, even doing group chats. Closed group chats support up to 100 people at once, with full E2E encryption, or open group chats without the encryption, but with an unlimited number of participants.
Session doesn't have some of the features that competitors like Signal or Telegram do. You won't find voice or video calls, for example. They are coming sometime down the road, but aren't available yet. If you need those features right now, then Session isn't for you. However, if you are good with chat-type communication in exchange for anonymity and privacy, keep on reading.
The company behind Session
The Session project was initially developed by a registered charitable foundation in Victoria, Australia called the LAG Foundation, LTD. Today, Session is a project of the Oxen Privacy Tech Foundation (OPTF). OPTF Ltd. is an Australian Registered Charity, with the goal of building, “open-source, metadata-free communications tools and apps that defend privacy in the digital world.”
As a charity, OPTF is unlikely to have any of the pressure to profit from user information that a messenger associated with a for-profit company (such as WhatsApp) would have.
Session security
As I mentioned earlier, Session started life as a fork of Signal messenger and its famous Signal protocol. That was a great starting point since many security experts consider the Signal protocol to be the most secure E2E encryption system available.
But the Signal protocol was designed to work on a system with centralized servers. It also collected more metadata than the Session team felt necessary. As a result, the Session team found themselves making more and more changes to their version of the Signal protocol. This approach didn't work out too well, and Session eventually decided they needed their own protocol designed specifically for their own needs.
The result was the Session protocol. The new protocol has made Session faster and more reliable while also supporting the company goals of anonymity and decentralization. While this changeover wasn't without cost (some ‘old' features had to be scrapped for compatibility with the Session protocol), overall it seems a big win for Session users.
Note: You can take a deeper dive on this topic by reading the Session White Paper.
Data storage with the Oxen network
Your data is stored on your devices. It has to be. There are no central servers for it to be stored on. But this raises an issue. What happens to messages sent to you when you aren't online? Those messages aren't lost, but to understand what happens to them, we need to talk a little bit more about the Oxen network.
Oxen is comprised of thousands of Service Nodes. Service Nodes are decentralized servers that pass messages back and forth through the network (among other things). In addition to providing the Tor-like message routing Session relies on, Service Nodes are grouped together into swarms.
Each swarm consists of 5-7 Service Nodes. Each swarm is responsible for managing the messages going to and from a particular set of Session IDs. The Service Nodes in the swarm work together to provide redundancy–if one Service Node goes offline, you can still send and receive messages normally. The Service Nodes in the swarm also hold a copy of any messages for the associated Session IDs when the recipient is not online.
Those temporarily held messages are deleted from all the Service Nodes once the message is delivered. And since all messages passing through the Service Nodes remain fully encrypted until they reach their destinations, the messages remain private and secure, even while they are temporarily stored in a Service Node.
The Session protocol uses X25519 keypairs, ED25519 public keys, libsodium (a fork of NaCl) encryption to ensure the security of your data. As far as I have been able to determine, your data is secure when you use Session messenger with its new Session protocol.
Third-party audits and testing
Session's desktop, Android, and iOS clients have undergone a code audit conducted by Quarkslab. This audit was completed in April 2021*. Without going through the entire report here, we can cut to the chase. Quarkslab found Session to be cryptographically sound. This is big news for Session and the OPTF and should make people much more comfortable with the idea of relying on Session for secure communication.
* If you want to read the whole report, you can download it here.
Transparency reports
Instead of its own independent Transparency Report, information related to Session is included in the OPTF's report. I can't comment on the kind of information that appears in such a report. That's because, as of the last time I checked (June 15, 2021), the foundation had received 0 requests from 0 jurisdictions.
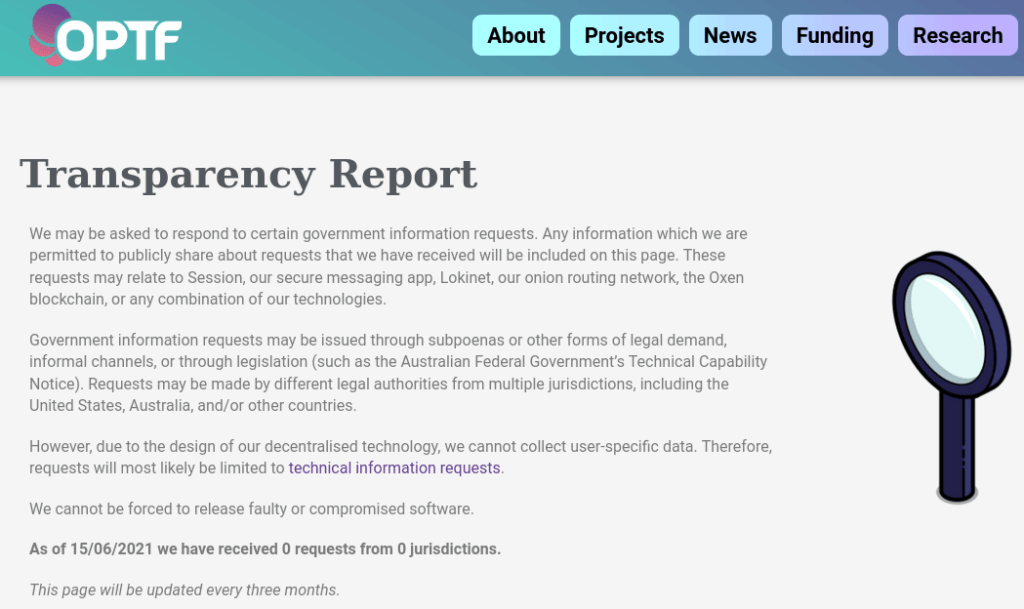
I assume that when and if the foundation does get an information request, the full details will be posted. Regardless, if you want to check out the page yourself, follow this link for the latest OPTF Transparency Report.
Using Session
I tested Session using the Android app and the Windows 10 desktop. After a rough start last year, Session now performs most functions smoothly. Multidevice support was pulled for a while, but it is now back in beta form. Hopefully it will be fully baked and tested in the near future.
Using Session mobile apps
You download Session for mobile from the usual stores. When you start it for the first time, the steps are a little different than they are for other messengers. Tell Session you want to create a new account and it will generate a long random Session ID for you. Make sure you copy that ID and store it somewhere safe. You can share your ID with other Session users to start a conversation.
Once you have your Session ID squared away, the app will offer you a choice of how to receive push notifications*. Fast Mode or Slow Mode.
* You can learn more about push notifications in the Session FAQ.
Fast Mode notifications can expose some metadata to Google, but the notifications arrive fast and always get there. Session recommends using Fast Mode notifications.
Slow Mode notifications ensure that none of your metadata gets exposed, but they take longer to arrive, and may not arrive at all.
Session also generates a recovery phrase you can use to recover your account if you need to. You can't restore your account using the traditional username and password combo because Session doesn’t have any central servers with information about your identity.
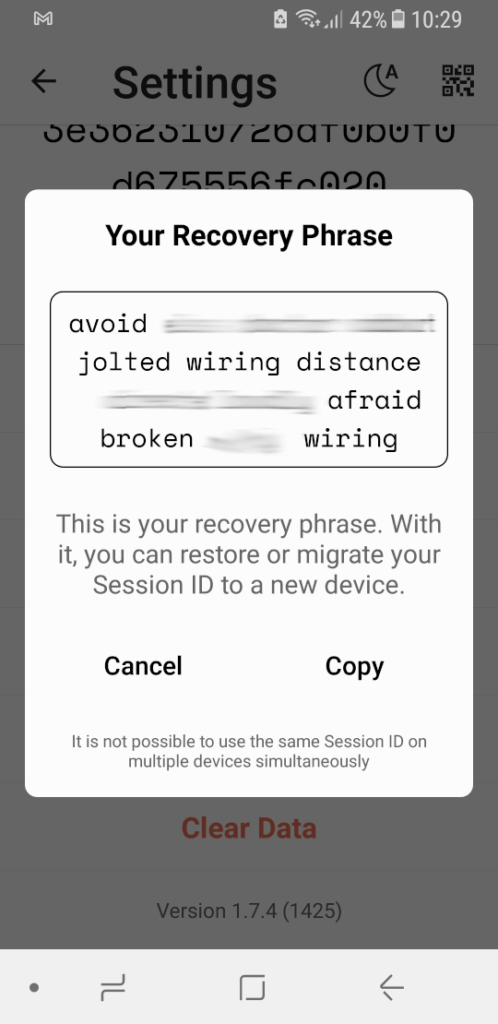
The recovery phrase is like a master key that Session can use to calculate your Session ID. Enter the recovery phrase into a different instance of the Session app and the app will regenerate your Session ID.
To restore your Session ID on a new instance of the app, launch Session and select Continue your Session. When prompted, enter your recovery phrase so the app can calculate your Session ID. You should be ready to go again.
Important: While restoring with your recovery phrase will get you back into your account, it cannot restore your contacts or messages. Those things are stored locally on your device and cannot be restored.
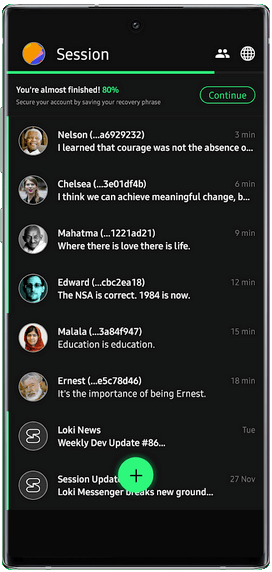
Actually using the Session mobile apps is easy. As of right now, you don't have some of the communication modes (video and voice calls for example) that you would have with some other messenger apps. But all the basics are here (text and voice chat, photo and file sharing, and animated GIFs). Everything that is implemented works well (remembering that multidevice support is still in beta).
Session also offers a number of interesting options under Settings. These include things like:
Screen lock – Lock the screen to protect against unauthorized use if someone gets their hands on your mobile device.
Incognito keyboard – Disable personalized learning by the keyboard (no sending what you type back to the mothership for analysis).
Read receipts – See if the recipient has actually read what you sent them.
Delete old messages – Trims the oldest messages from conversations once they reach the length you specify.
Chat backups – Create an encrypted backup of your chats for storage on an external device.
Theme – Not really a full theme, this gives you the option to set Session to Day, Night, or System default mode.
Using Session desktop apps
Session desktop apps are interesting in that they can stand alone. In other words, you don't need a mobile Session app to hook them up to. You can use them standalone, which is great for people writing reviews, among other things.
In fact, as I mentioned earlier, the ability to connect multiple apps (desktop, mobile, whichever) to the same Session ID is still in beta test. So we will concentrate on using Session desktop apps independently.
Downloading and installing the Session Windows desktop client goes as you would expect for any Windows app. Use the standard “install a Windows app” process. Launch the app to get your Session ID.
You'll have the option to create a new Session ID (or restore your existing ID), or log in to your existing account. You can also set a password to protect Session from unauthorized persons who get access to your PC.
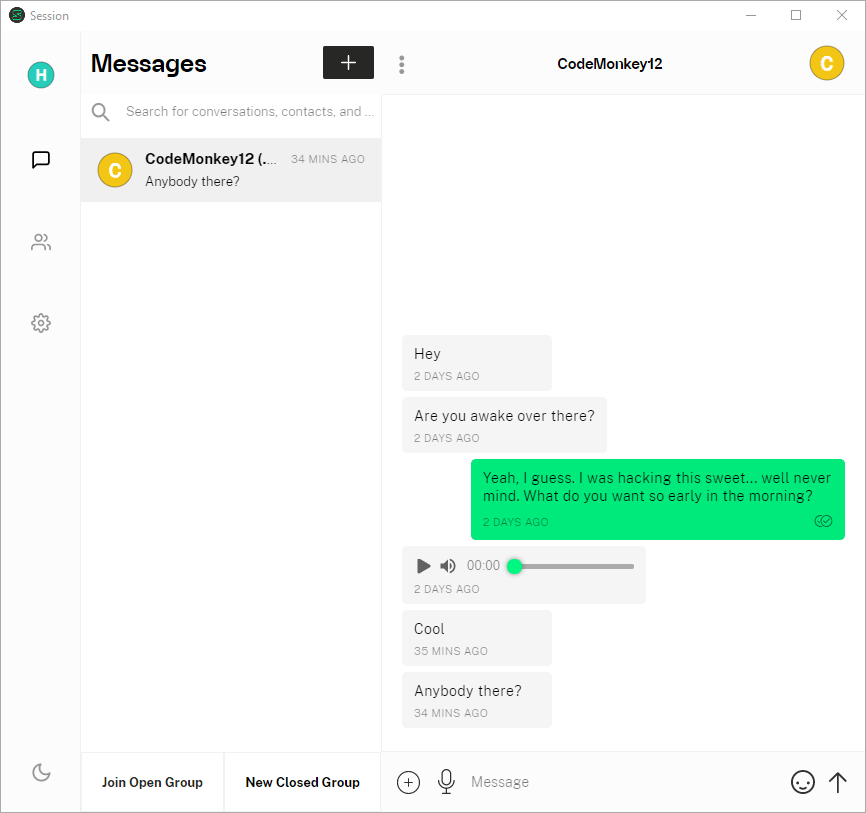
Get past all that and you will have an easier-to-use version of Session. This will be my preferred way of communicating with Session users once multidevice is ready.
As you can see in the image above, Session desktop (and mobile) support both open and closed groups in addition to individual chats. The Session developers continue to crank out both new and enhanced features all the time. You should consult their very educational blog to keep up with the ever-improving feature set of Session.
Session support
Session's support offerings are pretty bare bones. Like Telegram or Wire, the support comes primarily in the form of a FAQ page. But this one is pretty small, with only around 40 questions altogether. This being the case, it is very nice that Session does let you talk to a real, live, human being.
Session doesn't offer 24 hour live chat support. But they do let you contact support by emailing support@getsession.org. You can also join the official Session Feedback open group at: https://feedback.getsession.org using Session's group feature.
Session FAQ
Here are a few questions that have come up during research for this review.
Whether Session is safe or not depends in large part on what you mean by safe. Do you mean:
* Is Session messenger secure? Now that Quarkslab has finished their code audit we know that Session is cryptographically sound.
* Is Session messenger private? Combining its “no metadata” model with its use of the decentralized Oxen network for message handling, could make Session the most private messenger available.
* Is Session messenger anonymous? The design of Session messenger supports anonymous use. No personally identifiable information (PII) needs to be given away to use the system. At the same time, it is up to you to maintain your anonymity in your interactions with other Session users. The app can't prevent you from intentionally (or accidentally) disclosing PII yourself.
What is the Session protocol?
The Session Protocol is a secure, private, anonymous, and decentralized messaging protocol. The team at Session designed it to eliminate the problems they were having adapting the Signal protocol to their decentralized, anonymous architecture.
If you want to learn more about the Session protocol, here's a link to the technical explanation.
What is a Session swarm?
A Session swarm is a collection of 5 to 7 Service Nodes that collectively are responsible for storing messages for a predefined range of Session IDs. Service Nodes are community-operated nodes of the Oxen network.
Messages for your Session ID are stored in every Service Node of a particular swarm when they cannot be delivered to your device. Once a message is delivered, it is deleted from the swarm.
Are my messages stored on a blockchain?
While the Oxen network uses a blockchain, no Session messages are stored on it. Your messages are end-to-end encrypted and stored temporarily in a swarm until delivered, then deleted. There is no risk of your messages ever being stored on the blockchain.
Conclusion
Session messenger is an exciting attempt to bring anonymity and decentralization to the secure messaging world. After some tough challenges, the service seems to be working quite well now. If you can live with its current limitations (no voice or video calls) and don't mind being out there on the cutting edge, you should definitely give Session a try.
Session is a promising secure messaging app, but it isn't your only option. To see our list of the top options, check our our roundup of the best secure and encrypted messaging apps.
Securing your message traffic is important in today's world. But so is securing the rest of your online activity. You can easily secure all your internet devices with Surfshark, a fast, secure VPN that supports unlimited simultaneous connections. Learn more in our full Surfshark VPN review.
This Session Messenger review was last updated on January 6, 2022.
There is now Video/Audio it seems for Session. One would imagine that this aspect is ‘fully’ P2P (ip. address visible at either end) to work properly.
Although not independently audited and subject to much criticism from crypto ‘experts’ (when will this happen one wonders) from reading various commentaries/forums/etc, there is also Tox Chat platform. It is less developed and a lot less well (or at all) supported on some devices. It appears it is [always] P2P for everything and does not rely on service nodes [like Session] *once* ‘friends’ connections are established/accepted/setup.
When is a decentralised network not a decentralised network … is it when ‘session’ nodes get fewer and fewer … though if relied upon most minimally, is it an issue.
Session Messenger is interesting … as is Tox … as is [insert the next one on the scene]
how can I use this
Thank you for the great info. What about forward encryption? I’ve read that it is lacking in Session. Thanks again!
Hi Eric, Sir ! Thank you for this very instructive article. I have an additional question, please is a Session desktop client readily available to be installed on a Raspberry-Pi desktop (ARM Linux) ?
Yes, there is a Linux app, but I’m not certain if it will work in this situation:
https://getsession.org/download
Important: While restoring with your recovery phrase will get you back into your account, it cannot restore your contacts or messages. Those things are stored locally on your device and cannot be restored.
My last test it was possible to see all old chats again when I recovered the account. Scary!
Session is able to restore some account information upon recovery. It accomplishes this by periodically sending yourself a message with contact information, in the background. If you wait (about 2 weeks), the network will eventually discard the message, and no account information will be restored.