
What do you get when you mix annoying online ads with dangerous malware?
You get Malvertising. Malvertising attacks are an ever-present risk in today's world. You can get hit anytime, anywhere, with potentially devastating results.
In this comprehensive malvertising guide, we'll dive deep into every aspect of malvertising: what it is, why people do it, and how you can protect yourself. This isn't the most pleasant (or easiest to understand) aspect of online life, so get ready.
What is malvertising?
Malvertising is a delivery method for malware, PuPs (potentially unwanted programs). It uses malicious ads to get the malware onto your computer, smartphone, or other devices capable of displaying ads from the internet.
We know that may have sounded like a lot of gobbledy-gook, so let's define some terms:
Malicious ads: These are ads that are meant to do you harm. They might install trackers on your device to monitor your activities and send that information to the bad guys who created the tracker. They might send you to a website where various types of evil software await.
In the case of malvertising, they install malware directly onto your device.
Malware: Malware is malicious software. Depending on its design, malware can cause all sorts of trouble on your device. We don't need to go into all the different categories of malware. All you really need to know right now is that it is “bad” software that you don't want on your device.
PuPs: Potentially unwanted programs (PuPs) are exactly that — programs that you potentially would not want on your device. These are things like advertising apps, toolbars, and pop-ups annoying, possibly malicious code that aren't related to the software you downloaded and installed. One common delivery method for PUPs is to quietly bundle them with other software that you installed. When you install the good stuff, the PuPs get installed too.
Malvertising is another common PuP delivery method.
How does malvertising work?
Modern online ads are not always static images. They can be complex, active computer code that does numerous things. Because they are complex, clever villains have come up with ways to hide the fact that their ad is made up of malicious code designed to deliver malware.
Here are two examples of malvertising:
Sodinokibi ransomware was delivered through malicious advertisements (malvertisements) distributed through the PopCash ad network. The ransomware would then prevent access to data or other resources on the infected computer until the victim paid for restored access. The city of Riviera Beach, Florida was just one of the many victims.
RoughTed was a malvertising campaign that managed to generate hundreds of millions of visits to malicious domains and could bypass some ad blockers. It could hit devices running any operating system. Once the malware made it onto the device, it would attack with a variety of different techniques.
How can you protect yourself from malvertising attacks?
Protecting yourself from malvertising assaults requires some thought. There are a couple of parts to the problem. The first is to prevent the malicious ad or malicious website from installing something nasty on your device. That is priority #1.
We have some good ideas for how to do this, but malvertisers are clever. You can never be 100% sure they won't sneak something past your defenses somehow. Bad ads don't just appear in the bad parts of the internet. Malvertisers sometimes manage to buy ad space in quality advertising networks, meaning malvertising ads can appear anywhere.
So priority #2 is to be able to defeat whatever foulness the malicious advertising managed to get onto your device. In other words, just because you take all the recommended steps for stopping malvertising assaults on our devices, it doesn't mean you can skip installing antimalware software.
Now that we're clear on all that, here are our recommendations for stopping malvertising from ruining your day.
Priority #1: Block all ads!
Malvertising is the process of using malicious advertisements to put malware on your device. So it makes sense to start by blocking all ads.
Now you may be surprised by this advice. After all, lots of websites rely on ads to pay their bills. Won't blocking ads kill the internet? If you listen to the ad networks or lots of website owners, even thinking about blocking adverts is bad, probably immoral, maybe even criminal.
It is true that many websites depend on the income they receive from adverts. But so what? Ads have a large negative impact on your use and enjoyment of the internet.
Do you actually like seeing ads plastered all over web pages? Didn't think so. Ads are annoying, make pages load slower, and chew up your data plan on mobile devices.
Let's look at how much screen space this “news” website devotes to trying to sell you stuff. We find the adverts here particularly annoying since we are forced to support this company through our cable subscription. Anyway, here is a typical page with its ads:
A significant chunk of the screen space is occupied by ads, forcing some of the actual content off the screen while trying to draw your attention to the pretty ads. We do have to give CNN credit for displaying relatively classy ads. Many sites feature ads with flashing lights, embedded video, and blaring music that are frankly annoying as hell.
Now here is the exact same page, with adverts blocked from appearing:
The page is cleaner, with more actual content displayed, since there are no ads to dirty up the view. What you can't tell from the image is that the page loads much faster too.
Back to the main point
Getting a better online experience is great, but our real concern is killing malvertising. Most ad blockers (see “What the heck are Acceptable Ads?” in the FAQ to learn about the exceptions) prevent ads from getting downloaded to your device or processed by your web browser.
This is important, because some ads delivered by malvertising include malicious code that runs automatically if the ad gets into the browser. You don't have to click on the ad, and the ad might not even appear on your screen, but the malware (the payload) still gets delivered. A drive by download like this can ruin your day and you might not even know it happened.
So don't let the anguished cries of website owners and advertising industry lobbyists dissuade you. Every advert blocked is one less chance that some creep's malvertising campaign will give you major heartburn.
Some quality ad blockers
Ad blockers come in a few different varieties. To avoid turning this into a giant “best ad blocker” review, we'll talk about a few types of ad blockers and recommend our top pick in each type.
Browser extension ad blockers
The most common type of quality ad blockers are browser extensions. In this space, the extension that stands out is called uBlock Origin. Yes, it is a strange name, but the name is the result of a past ownership battle that we don't need to waste time on.
Note: The only thing you need to know about that old battle is that there is also an ad blocker named uBlock available. You do not want to use uBlock. uBlock Origin is the one you want. Period.
uBlock Origin can block a wide range of content, not just ads. However, it does come preconfigured to block ads and any other content from a large number of malicious domains that are know to spread malware.
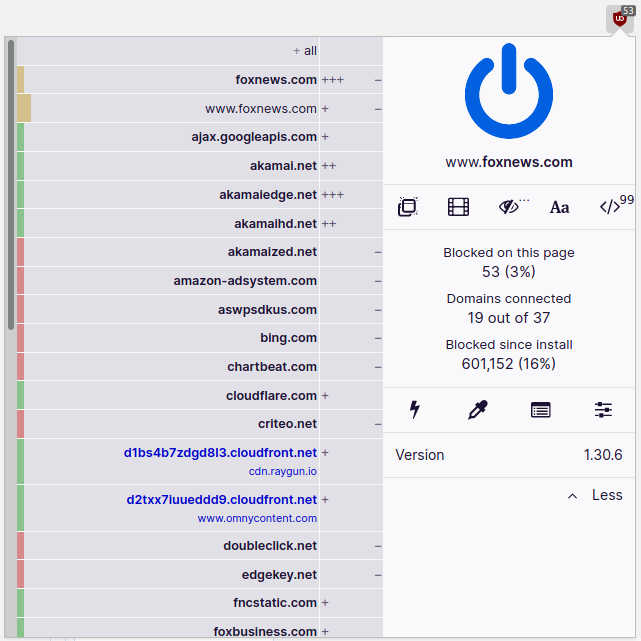
One of the things we particularly like is the way uBlock Origin shows you how many different items of content it blocked on any given page. It displays the number of items in a small grey box to the top right of the uBlock Origin icon.
For example, here is uBlock Origin doing its thing on the Fox News website. uBlock Origin found 53 items on that one page that it considered to be a malicious ad, or other types of content that should be blocked. We didn't investigate why a news website would try to load so much objectionable content into our browser. But as you can see in the following image, if you wanted to dig into it, uBlock Origin can display information about every item it blocks.
Another thing we like about uBlock Origin is that you can get great results by simply installing the extension. The lists of “bad” sites and other content that uBlock Origin uses to identify trouble are well maintained and should keep you out of trouble.
One thing we don't like about uBlock Origin (or any other browser extension) is that they can only protect your web browser. That's where the next category comes in.
Standalone ad blockers
Standalone ad blockers protect your entire device, not just your web browser. They plug into the stream of data coming into your device and prevent anything malicious from getting past them.
Our pick for the best standalone ad blocker is called AdGuard. It runs on Windows, Mac, Android, and iOS devices, which covers the bulk of computer users. The company also offer browser security extensions and privacy-related products. Be aware that the AdBlock browser extensions are available free of charge, while you will have to pay to get the standalone app.
AdGuard has a lot of additional capabilities besides its basic ad smashing power. Some of these might be particularly useful to you, but we need to keep this focused on the war against malvertising.
Like uBlock Origin, AdBlock will work fine right out of the box. That said, you can tweak and adjust its function to your heart's content. Just remember that your anti-malvertising goal is to wipe out any and all adverts that might try to get into your device while you play.
Ad Blocking DNS
What if you can't find an ad blocker for all your devices, or you would like to avoid the headache of installing ad blockers on your myriad internet-connected devices? A possible solution here is to use an ad blocking DNS service.
Us humans identify websites by names like CyberInsider.com. But our computers don't. They identify websites by IP addresses. Those IP address look like this: 45.79.181.19.
When you enter the human readable name of a website, your device sends a query to a DNS service. The DNS looks up the IP address in a huge database and returns that to your device. Your device uses the IP address to communicate with the website.
Some DNS services can also protect you against malvertising attacks by blocking malicious websites. We've tried out a number of these DNS services, and think AdGuard DNS is the best option in this space.
AdGuard DNS does a good job of blocking malvertising. Perhaps more important, they provide detailed instructions on how to configure devices to work with their service. Most people don't even know what a DNS service is, much less how to configure their smartphone or router to use one. The instructions AdGuard DNS provides make it relatively easy to switch from your current DNS service to theirs.
This service can be particularly useful if you have a ton of devices lying around your home or office that you need to protect. That's because you can use AdGuard DNS on your router too. Doing so protects everything on your network at once. You can see the instructions for setting this up here.
Note: Your Internet Service Provider (ISP) might not like you switching to AdGuard DNS. That's because many ISPs gather information about your DNS queries for their own use or to sell to third parties. Using AdGuard DNS instead of their default DNS not only protects your devices from malvertising, but denies your ISP this info. This is a security and privacy win!
We really like the idea of a service that provides ad blocking / malvertising protection to everything on your network. But using an ad blocking DNS service isn't the only way to get this done. There is an approach that not only blocks malvertising but greatly increases your privacy at the same time.
Consider using a VPN (Virtual Private Network) that has ad blocking built in. We particularly like the ad blockers in NordVPN and Surfshark. You can find out about both of them in our NordVPN vs Surfshark review.
Use a VPN with its own ad blocker
Some VPNs come with their own ad blockers built in. Using any good VPN protects your privacy against cyber criminals and and snoops of all persuasions. Using a VPN with its own ad blocker provides malvertising protection on top of those privacy protections.
Not up to speed on what a VPN does? The following is a quick explanation. Feel free to skip the explanation if you already familiar with how a VPN works.
How a VPN works
What a VPN does do is twofold: protect the messages that flow back and forth between your device and the internet, and hides your true IP address.
The VPN protects messages by encrypting them while they travel between your device and a VPN server. You can consider the portion of the connection where the messages travel encrypted as an encrypted tunnel. The encryption used for this tunnel is so strong that not even national intelligence agencies can crack it. Assuming your VPN is functioning normally, the message traffic between your device and the VPN server is secure.
Messages that travel between the VPN server and the target website are not encrypted. But before a message leaves the VPN server enroute to a website the VPN server replaces your IP address with the VPN server's IP address. As far as the website can tell, the message originated at the VPN server, not at your device. Since the destination website can't see your IP address, it doesn't know it is communicating with your device. The communication is private.
VPNs are powerful privacy and security tools. But neither VPN encryption nor hiding your IP address protects you against malvertising.
Why a VPN with ad blocking is a good solution
Things get much more interesting if you use a VPN that includes features that also protect against malvertising.
A VPN like NordVPN has a desktop client that when active can protect everything on the device. You don't have to worry about separately protecting each app that talks to the internet. Since you really should be using a VPN anyway, using one that also defends against malvertising will make your life easier.
Here are a few examples of VPNs that protect against malvertising for your consideration:
NordVPN CyberSec
Based on our testing, NordVPN is one of the best VPNs on the market. So it should come as no surprise that this VPN includes a potent feature that can stop malvertising campaigns dead. That feature is called CyberSec.
NordVPN CyberSec does a great job of blocking trackers, ads, and malware domains. It is not activated by default, but you can easily do so from within the NordVPN client:
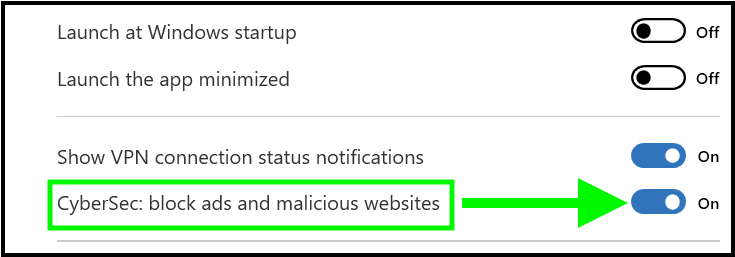
We found NordVPN's CyberSec feature to be very effective in our testing, and recommend activating it when you first set up NordVPN. It works well against malvertising since it blocks trouble in real time, including the third-party domains that are known to run malvertising campaigns.
To do its job, CyberSec uses real-time filters to stop DNS requests pointed at “bad” domains. This has both good and bad points. The good point is that it stops you from visiting dangerous domains altogether, keeping much of the bad stuff from ever getting to your device. The bad point is that it only works when you are connected to the VPN.
Note: NordVPN is offering a coupon below for SecurityTech readers and all plans come with a 30 day money-back guarantee. We also have a NordVPN review where we cover more info and test results.
NordVPN's Cyber Deal is live:
Get 69% Off NordVPN plus an additional 3 months Extra added to your subscription:
(Coupon applied automatically; 30 day money-back guarantee.)
Surfshark CleanWeb
Surfshark is another VPN that ranks high in our testing. It also includes a comprehensive tracker, ads, and malware domain blocker that stops malvertising campaigns. CleanWeb is Surfshark's version of CyberSec. It also blocks trackers, ads, and malware domains. And you can activate it from the VPN client just like CyberSec.
Check out our Surfshark review to learn more.
NordVPN vs Surfshark comparison for more details.
Perfect Privacy TrackStop
Perfect Privacy is another VPN service with a special feature that can protect you against malvertising attack. It is called TrackStop. It uses the real-time filters and the Perfect Privacy DNS system to do the job. While it in this, it is much like CyberSec or CleanWeb, there are a couple of important differences. One nice touch is that you can choose from several different lists, allowing you to block porn domains, fake news sources, even social media domains.
You choose the filters you want to use and turn TrackStop on and off from the Perfect Privacy website. If activated, TrackStop works whether you are using the VPN or not. That means you will be using the Perfect Privacy DNS whether you are using the VPN or not.
Private Internet Access MACE
Overall, we aren't big fans of Private Internet Access (PIA). We think there are definitely better VPN services available. That said, PIA has many users, who should be happy that the company created MACE. According to their knowledgebase,
MACE is a system developed by Private Internet Access to help protect our customer's privacy and security. Private Internet Access MACE returns IP addresses of unwanted domain names as an address that's not routable on the public internet.
In other words, when PIA detects that you want to browse to a malicious domain, the VPN modifies the URL of that address so that your browser can't go there. It seems a simple, effective solution.
Priority #2: Prevent or limit damage if malicious code does get onto your device
Stopping ads is the first line of defense against malvertising attacks. That's a worthy goal and if you implement some of the ideas we just discussed, you should be able to stop most, if not all attacks. Priority #2 is to prevent or limit the damage if somehow a malvertising attack succeeds. Implementing these ideas will do that, and will harden your devices against damage against any of the evil stuff that cybercriminals use.
Keep all your software updated
We admit it: keeping your software updated is a pain in the neck. Unfortunately, doing so is vital if you want your devices to function well and resist the latest cyber attacks. Enable automatic updates where possible, and make sure that you check for updates regularly on systems that can't or won't auto update for some reason.
What if you are running Windows 7 or some other old operating system? This can be really unpleasant. Microsoft and other operating system (OS) providers eventually stop supporting old versions of their OS. That makes old OS vulnerable to new malicious software since no one is providing patches or updates any more.
Your only secure options in this case are to update to the newest version of the operating system, or to switch to a new OS altogether. Given these two options it is easy to see why many Windows 7 users are moving to Linux, rather than Windows 10 with its pseudo-spyware reputation.
Turn on click-to-play in your web browsers
For a smoother browsing experience your web browser may be set up to play videos as soon as it loads a page. If that video is part of a malvertising campaign, your device could be infected before you know it. That's why turning on the click-to-play option in your web browsers is important. This option goes by various names, but its function is the same: it requires you to manually click before activating audio or video content.
This option is probably buried deep in the bowels of your browser's settings pages, so it may take some work to find it. And it may move around from version to version of the same browser.
Here's how to set the click-to-play option in Firefox 82.0.3:
- In the Firefox Preferences, select Privacy & Security.
- In the Permissions section, find the Autoplay option and click its Settings button. The Settings – Autoplay dialog box appears.
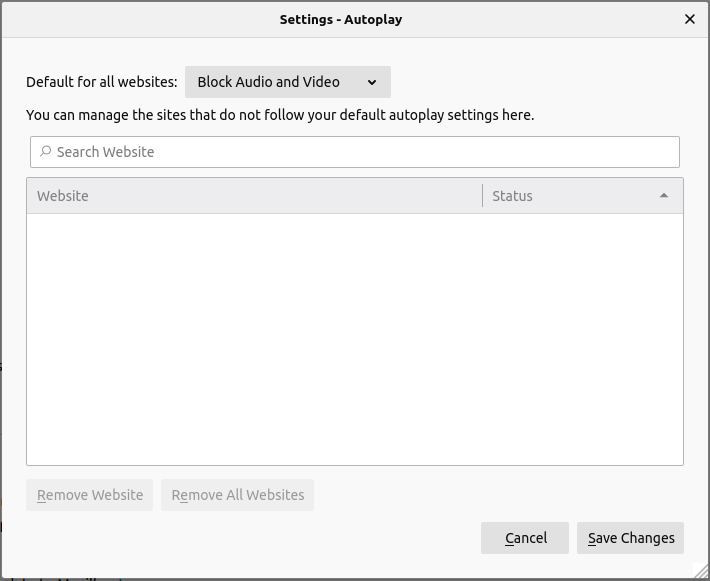
- In the Default for all websites dropdown list, select Block Audio and Video button at the bottom of the dialog box.
From now on, you will need to click to activate any audio or video content that appears in a browser window. It is a bit of a pain, but far less so than letting cyber criminals trash your device with malicious code embedded in some video.
Uninstall Flash and Java if possible
Many websites rely on Flash and Java. Unfortunately, they are both insecure products that can be easily exploited by malicious code. To maximize the security of your devices, it is best to uninstall both Flash and Java immediately.
Sounds like a great way to go, except for one point. There are still many websites that use Flash or Java and won't function without them.
The problem of Flash is due to go away soon. Current versions of Firefox no longer support it. Google Chrome stopped supporting it at the end of 2020, and other products are following suit. This is a perfect example of why you should update to the latest versions of the software you use. Upgrade to the latest Firefox, for example, and your Flash concerns are over.
And Java? Java isn't going away any time soon as far as we can tell. But if you activated the click-to-play option on your browser as we recommend, that should prevent Java from running unless you specifically launch it yourself.
Run antivirus software
You are probably already doing this, but if not, running antivirus software is another way to defend your device against any evil stuff that might be trying to get in. While there are many options out there, Windows Defender or something like Malwarebytes should be sufficient.
Consider encrypting important data
Suppose a malvertising campaign does manage to install something nasty on your device. If your important data is encrypted, the malware won't be able to do anything useful with it. Storing your most important data in a program like NordLocker could cause an attacker to look for an easier target.
Malvertising FAQ
Here are some of the common questions that come up when discussing malvertising. In this FAQ section we give you quick answers to each question. If you want more details on any of these topics, you will find them in the body of the article.
What is malvertising?
Very simply, malvertising is advertising that does bad stuff to your computer or other device. There are various types of malvertising that do various evil things, but they all involve advertisements that do bad stuff.
What's the point of malvertising?
The main reasons for malvertising attacks seem to be:
- To steal your ID and other personal data
- To steal your financial data
- To steal your contacts
- To seize control of your computer for criminal activities
What's the difference between adware and malvertising?
It is easy to get confused about the difference between adware and malvertising. We're going to clear up that confusion right now.
Adware is a type of malware (malicious software) that displays ads on your screen. These ads aren't related to the website you are visiting, and may promote dubious or illegal products. It may also log your browsing activity and sell that information. There are many ways that adware can get onto your device.
Malvertising is a way to attack your device. It uses ads to get malware onto your device. It can be used to deliver any type of malware, including adware.
Why would an ad network distribute malvertising?
These are probably the two main reasons that ad networks distribute malvertising:
- They don't know they are doing it. Some people who create malvertising go to great lengths to hide the fact that their ads are, in fact, malvertising. There are many techniques a clever crook can use that make it difficult to discover what they are up to. Smaller or less technically sophisticated ad networks don't always have the resources to detect the trickery.
- They don't care. While most ad networks are concerned about their reputation and do what they can to stop malvertising, not all networks do. There are immoral ad networks that don't care what your ad does, as long as they get paid.
Should I feel bad about blocking ads?
No! While there are arguments for not blocking ads, they aren't valid. We explain why in the, “Use a strong ad blocker” section of the article.
What are Acceptable Ads?
One of the odder things going on in the world of ad blockers is the Acceptable Ads program. While you would expect your ad blocker to block every ad it can, several of them make an exception for this program.
We don't want to waste your time (or ours) going through the whole story. The key takeaway here is that the Acceptable Ads program pays certain ad blockers to allow “Acceptable Ads” to appear while blocking ads that aren't part of the program.
We assume the program does what it can to ensure that the ads accepted into the program are safe. Even so, this seems like a really bad idea to us. Every advert blocked is another potential malvertisement that can't hurt you.
Because they participate in the Acceptable Ads program, we recommend you avoid the following ad blockers:
- AdBlock Plus and AdBlock Premium products
- uBlock products (not uBlock Origin)
- Crystal products
Can malvertising hurt me if I never click on ads?
The mere fact that an ad appears on your screen can in some cases lead to a malvertising attack against your device. That's the joy of drive by downloads.
What is a drive by download?
A drive by download is when an ad can put malware on your device, even if you don't click the ad. They are pretty horrible, but we do have some suggestions for how you can prevent them and minimize the damage if they do get through your defenses.
Can my phone get infected too?
Yes, your phone can get infected, and your tablet, and most any other device that you can run a web browser on. But don't worry. Most of the information in this article applies to your phone as well as your computer and other devices.
Conclusion on malvertising
Malvertising is the term for a range of tools that use advertisements to deliver malware to your devices, usually through your web browser. Unlike the early days of this plague, today some malvertising campaigns can infect your devices even if you don't click on a malicious ad.
Protecting your devices against these assaults is important. In this article we discussed malvertising in detail, including a few examples of “famous” malvertising campaigns from the past.
The bulk of the article covered two priorities:
Priority #1 – Preventing malvertising from placing malicious code on your devices
Priority #2 – Hardening your devices to withstand the assault if a malvertising campaign or other nasty exploit somehow gets malicious code onto your devices.
If you attend to both of these priorities, you will go far toward making your devices secure against malvertising attacks. Good luck.
This malvertising guide was last updated March 12, 2024.
Leave a Reply